Hierarchical Deterministic (HD) Wallet
By Sumi Maria Abraham, Research & Training Engineer Kerala Blockchain Academy
Wallets are something that always stays closer and pampered. Be it the wallet we carry in our bags or the payment wallets we use for exchanges. They are incredibly dear as they maintain our assets. Similar is the case of a blockchain wallet. A blockchain wallet allows users to manage different cryptocurrencies — for example, Bitcoin or Ethereum. It is software that helps someone exchange funds quickly. Here, the transactions are cryptographically signed; the user’s privacy and identity are preserved. Blockchain wallets do not store coins, unlike our traditional wallets. Instead, they keep the keys of the cryptocurrency user. The coins are stored in the blockchain. The relationship between keys-coins is similar to that between debit/credit card- fiat currency managed by banks. Like, we conduct transactions using debit/credit cards, cryptocurrency transactions are conducted using a pair of keys: public key & private key.

In a blockchain wallet, the user’s account address is derived from the public key, and anyone who knows the public key can transfer the funds quickly. However, the private key acts like a PIN kept secret as it’s used to transfer funds from an account.
Wallets are classified based on how their keys are generated. They can be non-deterministic(random) wallets or deterministic (seeded) wallets. In random wallets, the keys are randomly generated values. However, maintaining a random wallet is problematic since a user should keep a backup copy of all the keys.

Here comes the seeded wallet as aide. Here, the keys are mathematically generated from a seed, which is a random alphanumeric number. The seed will have an alternate representation of 12–24 English words called the seed phrase, which is user-friendly compared to the alphanumeric representation. An example is shown below
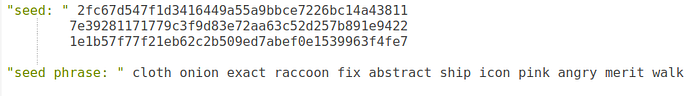
Under seeded wallets, only seed needs to be backed up since the remaining keys can be retrieved from it. So a single value can represent thousands of keys stored in a wallet.
Hierarchical Deterministic Wallet (HD Wallet)
HD Wallets generate keys from the master key in a hierarchical manner, following a tree-like pattern.

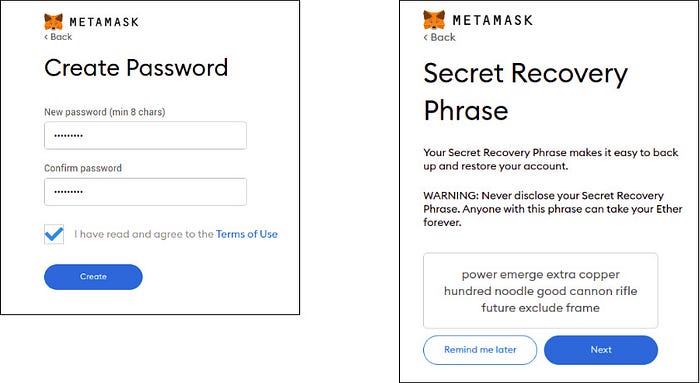
Now let us see how keys are generated in HD wallets. For that, we are taking MetaMask. MetaMask is the commonly used HD wallet to interact with the Ethereum blockchain.
Let’s go ahead and understand HD keys based on creating a MetaMask Wallet using its browser extension. Detailed installation procedures and settings are omitted as we discuss steps related to key generation alone. Check this link for the MetaMask installation demo video.
Download the MetaMask from here. Complete the signup process. You will be redirected to a page that has the seed phrase.
Well, How did you get the seed phrase ?. When you sign up, let’s see what MetaMask does at the back end.
Initially, a random number will be selected as the root seed. The root seed will undergo certain mathematical transformations, including hashing. The resulting value is used to construct the seed phrase by choosing a sequence of 12–24 words from a BIP39 word list. The number of words in the seed phrase depends on the size of the root seed. The user should keep the Seed phrase secret since the wallet can be recovered using it. Once the seed phrase is generated, MetaMask will prompt the user to re-enter the seed phrase.

Next, is the generation of the master key. The root seed is fed as input to a hash function and, the resulting hash is used to create a master private key and a master chain code. The hash function consists of multiple stages of mathematical operations. The concept of hashing is explained here.
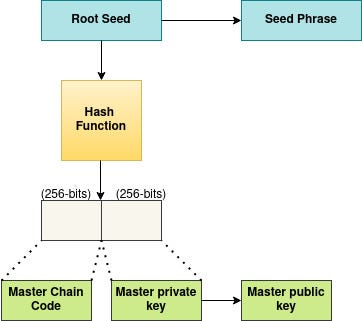
The master public key is derived from the master private key, and the account address is generated from the public key.
The master key is used to generate a sequence of child keys. Each of these child keys can act as a parent key and generate a series of keys, calling grandchildren of the master key. This can be repeated any number of times, expanding the tree structure by increasing the number of levels. Here chain code is a value used for generating child keys (not to be confused with chain code in Hyperledger Fabric, which refers to a program).

Changing the index value allows creating the other children in the sequence. In Bitcoin, each parent key can have 2 billion children keys.
Only the seed phrase, account address and private key will be revealed to the user. The rest of the values are used for back-end processing alone.
Once you create a MetaMask wallet, an account will be generated by default.
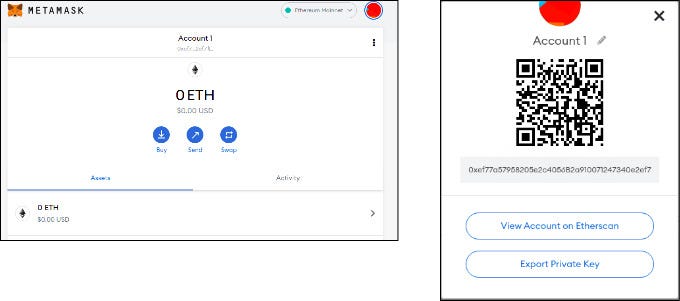
There is an option to export private key, which shows the private key after confirming the password. The private key will be required if an account needs to be imported to another wallet.
Further accounts can be created using the options provided in the interface.
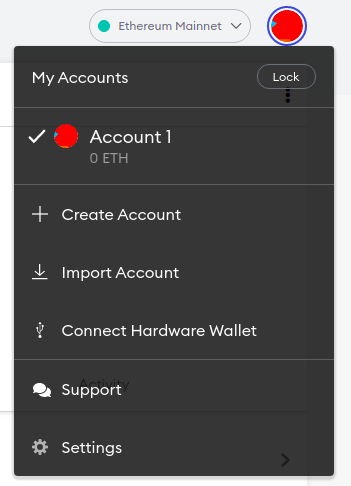
You can either create a new account using MetaMask or import an existing account by specifying the private key.

If anyone tries to create a wallet in another system using your seed phrase, all your keys can be retrieved using that seed phrase. So do not reveal the seed phrase to anyone.
There are various types of deterministic wallets. So what is the benefit of using HD Wallets ? Let us analyze it based on the concepts discussed.
The key generation’s tree structure can reflect the organizational structure in HD wallets. Each branch or account can be assigned to specific departments or purposes. It also allows a user to create multiple public keys.
The public-key, private-key, and account addresses are indistinguishable since all follow alphanumeric format. HD wallets also provide options for creating public keys without accessing their corresponding private keys. It is, therefore, useful in e-commerce applications like online shopping websites, where a separate address is required for every transaction. Also, HD wallets can be used in secure servers which use account addresses to read or receive funds, without providing an option to send funds from an account. But if an adversary manages to leak a child-private key, it can be combined with chain code to generate all the private keys of child nodes and the parent-private key. This situation can be avoided by using the private key to derive the chain code, which does not reveal any child’s private keys.
HD wallets provide robust privacy as separate keys can be generated for each transaction. Since you have multiple addresses, others in the network will not be able to figure out which addresses are linked to you. Your accounts remain secure as long as the master key is kept secret. If you lose your recovery phrase, your coins may get lost forever.
Some examples of HD wallets are Electrum, Trezor etc. If you are interested in trying the key generation, check out this link.
